The passwordless story is not over. A while back, I summarized the possibilites we have to reduce the usage of passwords with Azure AD. You can find this post here: https://chrisonsecurity.net/2019/07/28/going-passwordless-with-azure-active-directory/
This topic will become more and more important in the future, so I decided to to a follow up to cover some additional things.
FIDO2 is here to stay
Microsoft already pushed Hello for Business for quite some time. The Authenticator App for passwordless sign-in is also a big plus. However, the biggest chance is the support for FIDO2 tokens. And personally, I think this will solve many use cases and gives security-aware companies a familiar feeling – they have already been using similar technology like smart cards or other tokens already.
In the following paragraphs I talk about my experiences with different FIDO2 keys.
Note
The keys covered in this post are just used as examples to demonstrate the possibilities with passwordless authentication. None of the manufacturers paid for this coverage. These are just the devices I have lying around.
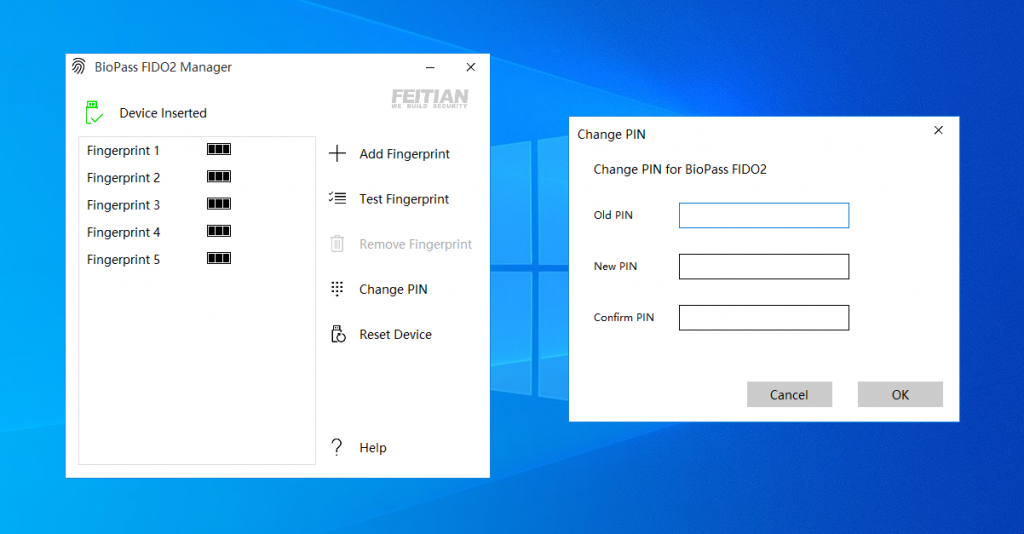
Feitian BioPass K27
I’ve been using this Feitian BioPass for quite some time now. The fingerprint reader makes it very comfortable to authenticate. Especially if devices have no built-in biometrics this is an advantage.

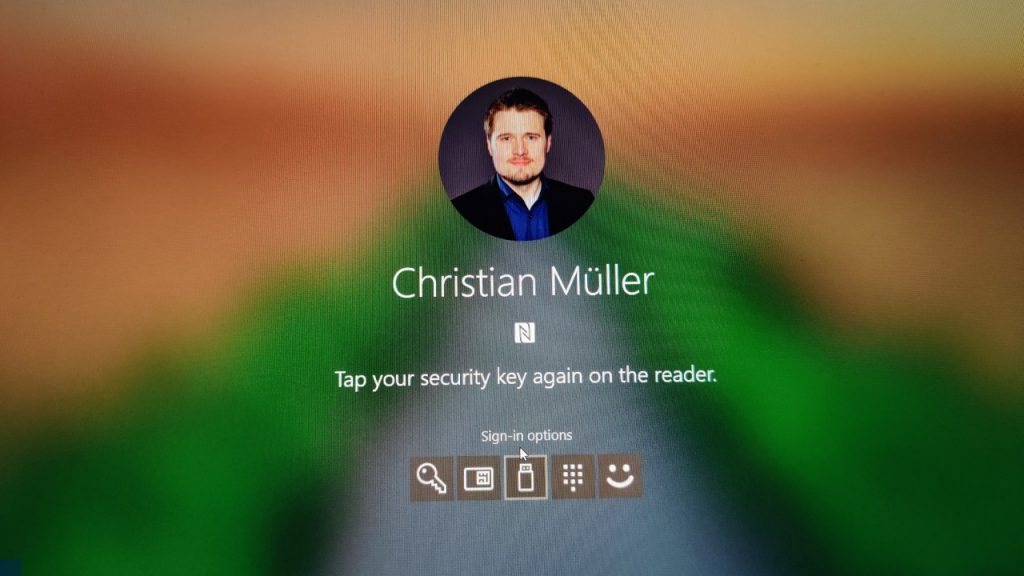
yubico YubiKey 5 NFC
The YubiKey 5 NFC is a quite familiar looking yubico key.
Second to its USB-A connector it also supports NFC. That way you don’t need to plug it in to devices that also support near-field communication.
My Lenovo X1 Carbon does so using an NFC antenna at the top of the touch pad:
Once you position the key close enough, Windows 10 will prompt you to enter the PIN. Of course, this also works on other devices. FIDO2 is not Microsoft exclusive after all.
yubico YubiKey 5C
This is the YubiKey 5C. It is very small and very easy to transport at a key chain e.g. Due to its USB-C connector it can be used on desktop as well as mobile clients. Unfortunately, Microsoft does not support authentication on Android or iOS using FIDO2 tokens at the moment.
The 5C is so small, that even the touch sensors had to be moved to both sides. These just register touch however, they are not fingerprint readers.
Which FIDO2 key is the best?
To be honest? I don’t care. They all do their job and they do it reliably. If you want biometric authentication the Feitian BioPass line-up is the obvious choice. Besides that, they deliver what they are meant for: FIDO2-compatible authentication.
Here you can see all of them side-by-side:

The point is: their technological baseline is always the same using FIDO2 as an industry standard. Which one is right for you depends on use cases and required form factors.
Managing FIDO2 keys
Of course, FIDO2 key have to be linked to a certain account to begin with. I already coverd those steps in my previous post: https://chrisonsecurity.net/2019/07/28/going-passwordless-with-azure-active-directory/
What if you want to configure additional parameters like changing the PIN of the device or the registered fingerprints? Here are some solutions.
Feitian publishes the BioPass FIDO2 Manager on the Windows Store: https://www.microsoft.com/store/productId/9P2ZJPWK3PXW
It can be used to change the key’s PIN or fingerprint, as well as to reset the device. Testing a fingerprint you already configured is also a nice option:
However, most of this can also be done with Windows 10:
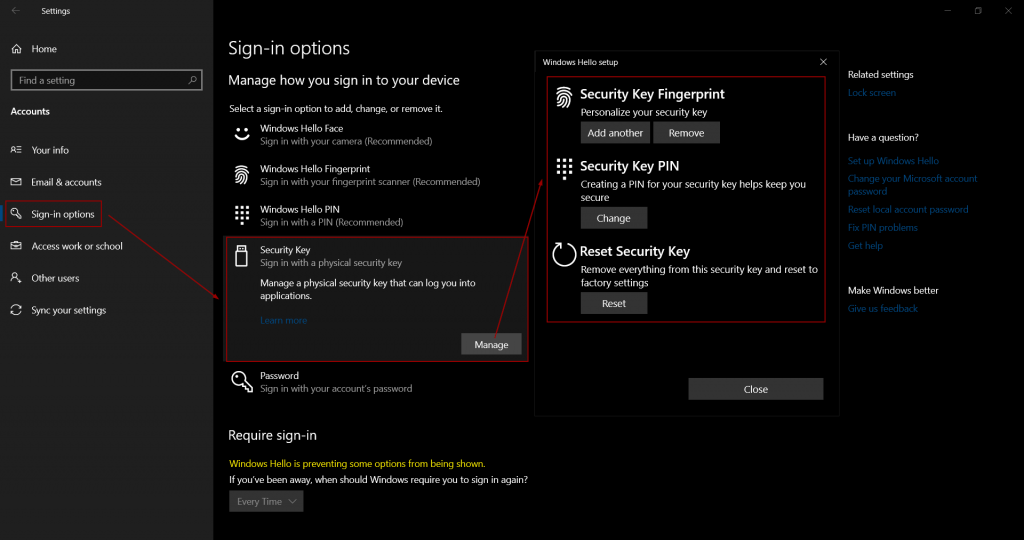
In a corporate scenario you should make sure that employees know how to work with their keys and how to master common tasks on their own.
Passwordless: the “bootstrap problem”
There is one open topic that remains unsolved with the Microsoft passwordless strategy: starting as a new user without any password right from the beginning. Let’s assume a user gets their new device on their first day at a new employer.
The company is using Windows Autopilot to provision Windows 10 devices. Once the user joins the device to their user profile, Azure AD enforces MFA for the Azure AD Join. However, at this point the user does not have registered MFA factors yet. This can be mitigated by an administrator who sets authentication information for the user, e.g. by provisioning a mobile phone number to the user’s account. Now the user could complete the MFA challenge.
But: being able to complete this challenges is no passwordless scenario as it still requires entering a password to begin with. In a passwordless world, the user shouldn’t even know it. The solution: use passwordless authentication via the Microsoft Authenticator app. This could be a suitable scenario, however, there is also a problem: in order to activate phone sign-in via the Authenticator app, the mobile device must be registered in Azure AD. At the moment, this cannot be completed without entering the account’s password. So, the bootstrap problem remains for now.
Passwordless is the future
Basically, I can just repeat my verdict from part 1 of this post:
Yep, there are still some limitations regarding the passwordless journey. However, it is already possible to use it for a majority of scenarios. I am very sure that in a few years using your password will be a niche scenario. Even today, I am hardly using my corporate password at all.
I’m pretty sure all limitations will decrease over time.
Thanks for reading!
Chris