Microsoft Ignite 2020 has started and with it we already got quite some announcements from the security perspective. In this post, I’d like to give a short roundup of everything that was announced regarding security operations.
Microsoft 365 Defender
We have a new name for a product family: Microsoft 365 Defender. M365 Defender is an XDR (eXented Detection and Response) solutions that consists of the following products (yep, there’s some renaming going on):
- Microsoft 365 Defender (old name: Microsoft Threat Protection).
- Microsoft Defender for Endpoint (old Name: Microsoft Defender Advanced Threat Protection).
Short: MSDE - Microsoft Defender for Office 365 (old name: Office 365 Advanced Threat Protection).
Short: MSDO - Microsoft Defender for Identity (old name: Azure Advanced Threat Protection).
Short: MSDI
Please excuse me while I update documentations, concepts, and service descriptions.
Besides that we also get new features:
- Mobile Threat Defense in Microsoft Defender for Endpoint for iOS now in preview which will be available in the upcoming weeks. It includes:
- Anti-Phishing to block unsafe websites (via Defender SmartScreen service)
- Block unsafe connections: SmartScreen will also block unsafe connections established by apps
- Custom indicators can be applied to allow or block URLs and domains
- Check out the documentation for more info: https://docs.microsoft.com/en-us/windows/security/threat-protection/microsoft-defender-atp/microsoft-defender-atp-ios
- The Android version moves to GA
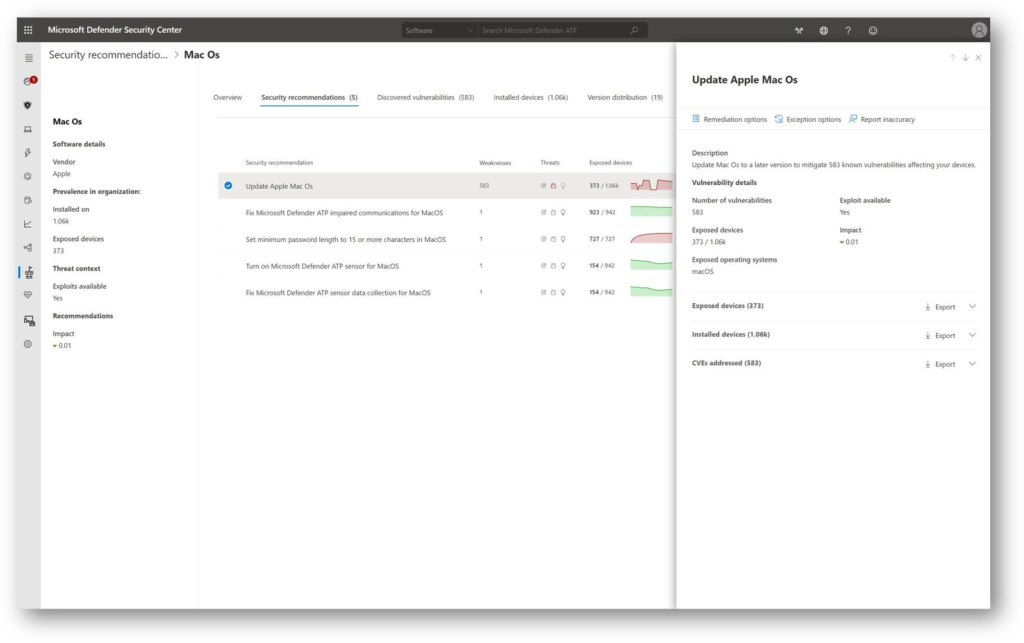
- Threat and Vulnerability Management will come to macOS in public preview
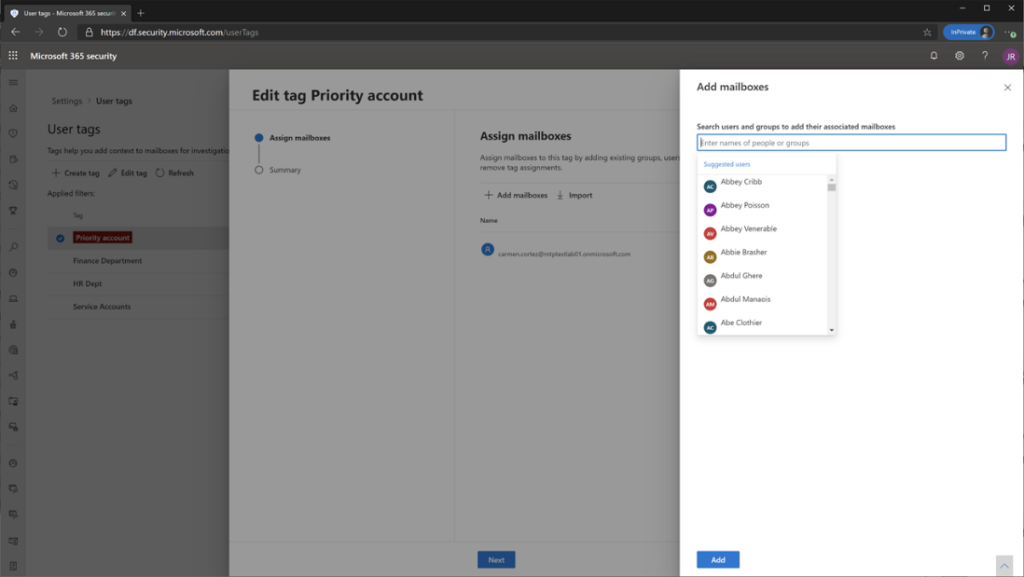
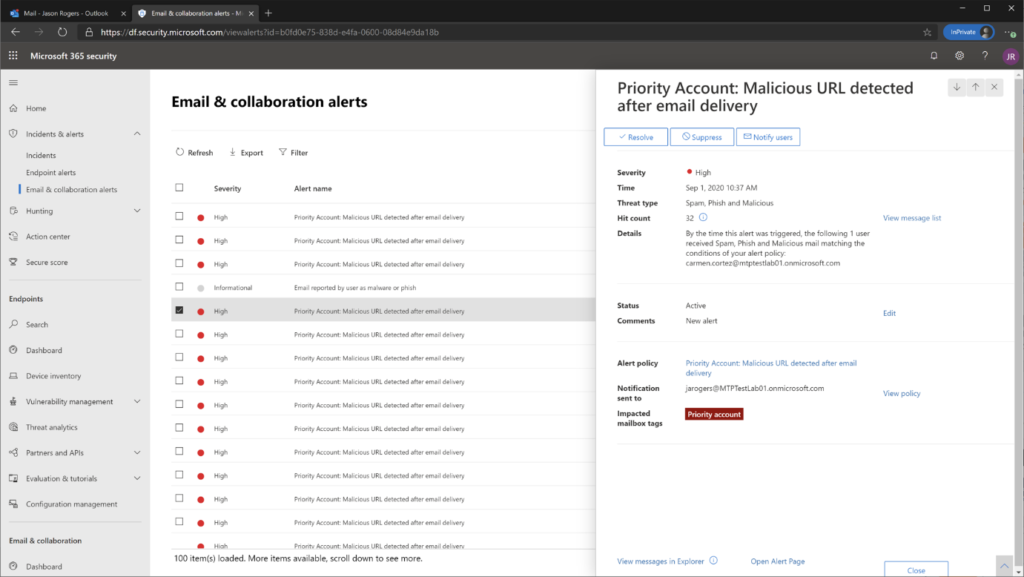
- Priority Account Protection for Microsoft Defender for Office 365 gives you the option to flag critical users.
Azure Defender
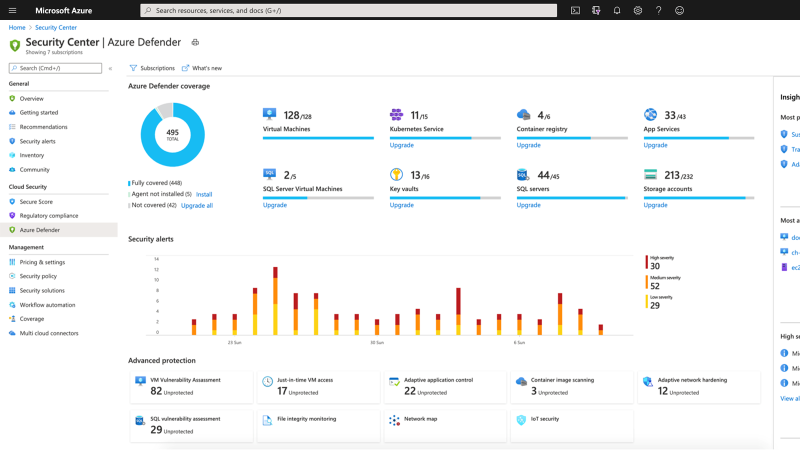
Azure Defender offers XDR capabilities for multi-cloud and hybrid workloads. It evolved from the Azure Security Center, which will still be available as the access panel for Azure Defender.
Again, some renaming:
- Azure Defender for Servers (old name: Azure Security Center Standard Edition).
- Azure Defender for IoT (old name: Azure Security Center for IoT).
- Azure Defender for SQL (old name: Advanced Threat Protection for SQL).
But also new features:
- Updated experience to make it easier to view resource protection status
- Added protection for both on-premises and multi-cloud SQL servers, and for virtual machines in other clouds
- Improved container protection
- Integration of CyberX (recently aquired by Microsoft) into Azure Defender for IoT
Azure Sentinel
Azure Sentinel remains the tool of choice to extend Microsoft Defender with data from other security solutions like firewalls, on-prem servers, and other security solutions. At Ignite, the following features have been announced:
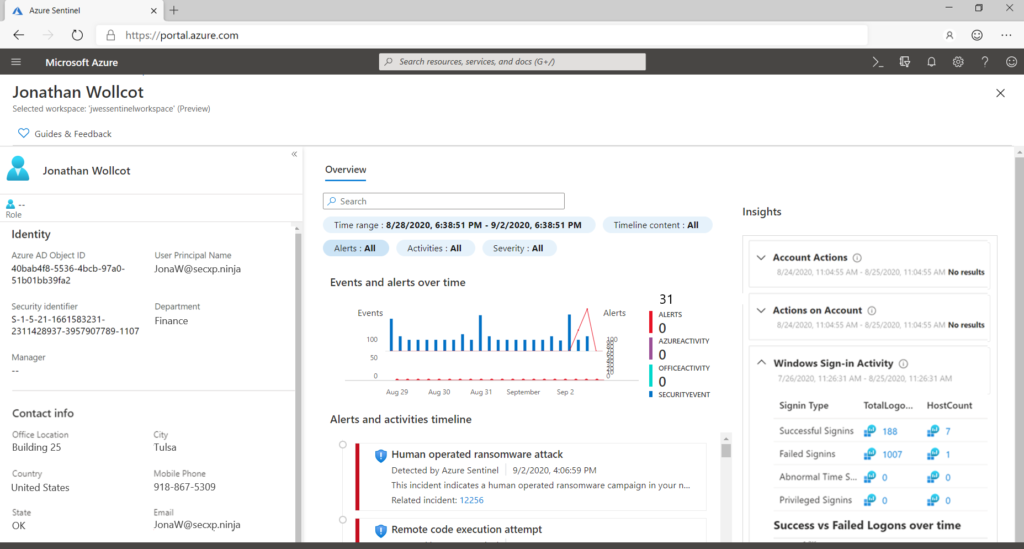
Entity behavior analytics
Gives you all related information to an account that might be compromised or a malicious insider
Threat intelligence
You are now able to add and track threat indicators that can be used for threat intelligence lookups

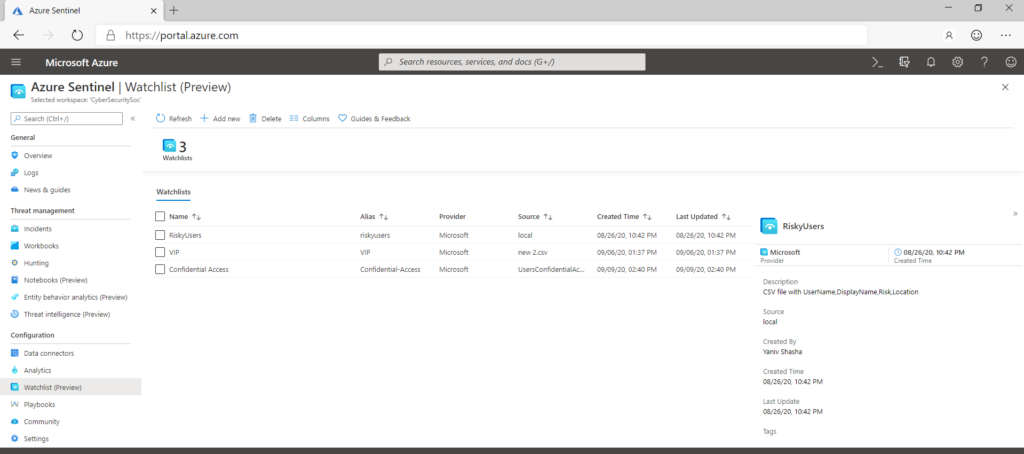
Watchlists
Allows to import collections of external data to correlate those with security events and insights from Azure Sentinel. Watchlists can be used in analytics rules, threat hunting, workbooks, notebooks, and within standard log queries.
Data collection
- The Office 365 connector now supports Microsoft Teams activity logs
- In the coming weeks a new connector for raw log data from Microsoft Defender for Endpoint will be released
- The CyberArk connector is now available
- Logstash: Azure Sentinel can be used as the output for Logstash
- Better visibility for Azure networking with the connectors for Azure Firewall, Azure WAF, and Azure DDoS
Machine learning
- Azure Sentinel notebooks are now using the Azure Machine Learning service
- Build-Your-Own Machine Learning: new framework for custom machine learning use cases
IoT
Microsoft recently acquired CyberX. Data will be integrated with Azure Defender for IoT which will then also be available to Azure Sentinel through the existing IoT connector.
That’s it for Microsoft Ignite 2020 security news. Thanks for reading!
Chris
Note
Please note that all content on this blog is provided ‘as is’ without any warranty.
Image sources:
- https://techcommunity.microsoft.com/t5/azure-sentinel/stay-ahead-of-threats-with-new-innovations-from-azure-sentinel/ba-p/1693166
- https://www.microsoft.com/security/blog/2020/09/22/microsoft-unified-siem-xdr-modernize-security-operations/
- https://techcommunity.microsoft.com/t5/microsoft-defender-for-office/announcing-priority-account-protection-in-microsoft-defender-for/ba-p/1696385
- https://techcommunity.microsoft.com/t5/microsoft-defender-for-endpoint/microsoft-defender-for-endpoint-adds-depth-and-breadth-to-threat/ba-p/1695824
